iOS SSL Pinning: Important Facts
We blindly trust software with sensitive information, such as passwords and personal details, with everything online. Almost everybody uses apps without thinking twice, which is why most of us take them for granted. According to internet security statistics, cybercrime has been committed an average of 2,244 times daily. This depicts the gravity of the situation and the need for stricter security measures. And this is where iOS SSL pinning comes into play.
Security is integral to any device/app/software we work with. The user’s data integrity is given supreme interest while building something because, without protection, the application is of no use. Information is communicated between the server and the client to transfer the necessary data, which needs to have a layer of protection so that cyber-attacks can be prevented.
Secure Socket Layer( SSL) is a security protocol that protects the information sent between two parties, from server to server or server to client. With SSL encryption, the protocol is encrypted, making information indecipherable to anyone with malicious intentions. HTTPS websites have the SSL protocol implemented after obtaining the SSL certificate. The default protocol, HTTPS, is used by 79.6% of all websites. These ensure that the user is dealing with a secure website and verifying its authenticity.
Usually, the application accepts any server request with an SSL certificate without any criteria to strengthen the filtering procedure. iOS SSL pinning is done to increase the security of iOS apps and prevent cyber-attacks.
Further Read: How To Prevent Threats For Enterprise Application Development?
How Does SSL Work?
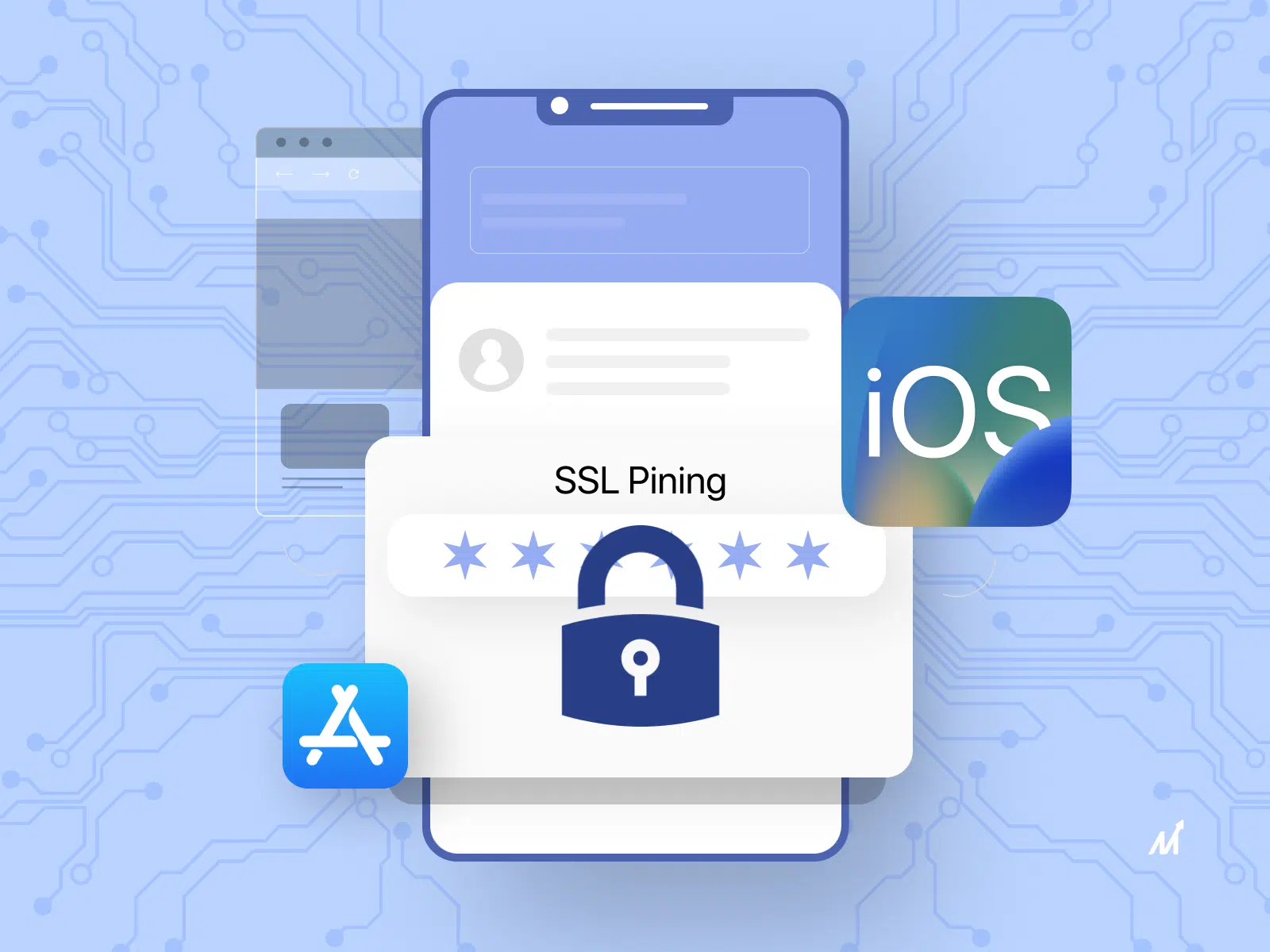
SSL works on the principles of cryptography, using the concept of asymmetric and symmetric cryptography. It uses keys for encryption and decryption, which are sued to safeguard data transfer.
In asymmetric cryptography, also known as the SSL handshake and happens at the beginning, two keys are involved: the public and private keys. The sender encrypts it with the receiver’s public key, which is then decrypted on the other end by the receiver using their private key, which is mathematically related to the public key by some algorithm such as RSA, ElGamal, etc.
Symmetric cryptography, on the other hand, only requires one key, and it’s used after the SSL handshake to generate the session key for data transfer. Both sender and receiver have the key, which is only known to them.
For initiating the whole process, a ‘client hello’ message is first sent from the client’s side containing details like the client’s SSL version number, session-specific data, etc. A similar ‘server hello’ message is sent from the server’s side, containing the server’s SSL version number, session-specific data, and an SSL certificate with a public key.
After the server’s SSL certificate has been verified by the CA (Certificate Authority), the client sets up a connection to the server.
The client creates a session key, encrypted by the server’s public key, and then sent to it. When the server decrypts the session key with its private key, an acknowledgment is sent to the client. This session key aids in the data transfer process, and the private and public keys are never utilized again.
Types Of iOS SSL Pinning Methods
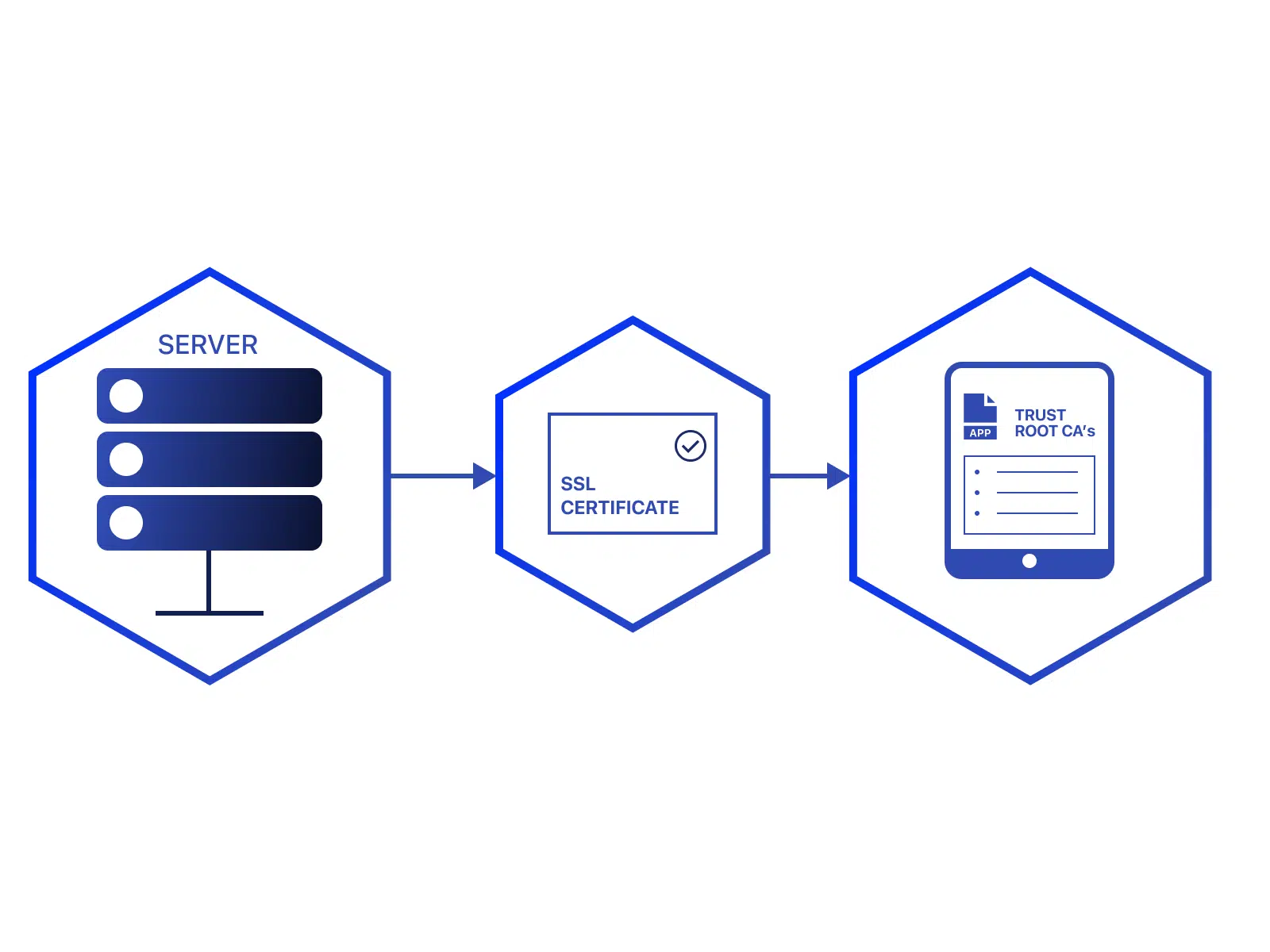
SSL pinning combines and attaches a list of trustworthy certificates to the application during the development phase and compares it whenever a server request comes during runtime. Only the trusted, pre-defined certificates are authorized with this technique. There are mainly two ways of SSL pinning methods:
1. Embedding The Certificate
This involves extracting the server’s certificate and then embedding it onto the app, which the network layer can later compare.
2. Embedding The Public Key
For later comparison with the server certificate’s public key, only the public key is embedded in the code or app instead of the entire certificate.
There are three types of certificates used during the SSL pinning methods:
1. Leaf
If the pinned certificate is expired or broken, it will disrupt the application till it’s updated. Thus, this has a significantly less expiration time.
2. Intermediate
This requires trust in the CA. As long as the certificate comes from the same provider, any changes to the leaf certificate will not affect the application.
3. Root
This is based on the chain of trust. If the certificate does not match during validation, it checks the issuing CA to see who was authorized until they reach a trusted CA at the top of the chain.
Implement iOS SSL Pinning: Securing iOS Applications
A few methods with which SSL pinning can be implemented are:
1. NSURLSession
During the case of an authentication request from the server, the client first requests it for their credentials. The server’s certificate is then compared with those saved in the app bundle, and if it matches, the authentication is granted.
All the checks are done manually in this method to implement SSL pinning. An NSURLSession object is first initiated, and the dataTaskWithURL: completion handler: method is used then for the SSL pinning test.
2. Alamofire Certificate Pinning
This is a popular HTTP networking library in the Swift language(used for iOS native development). It comes with the built-in functionality of SSL pinning. AlamoFire has the ServerTrustPolicy.certificates bundle method, which returns all the certificates within the bundle. This approach requires pinning only the pre-defined domains instead of all domains.
Issues Associated With iOS SSL Pinning
iOS SSL pinning is still looked at apprehensively by some app development companies due to various reasons:
-
It has a highly complex implementation during development, which might delay the cycle due to repetitive code rewriting.
-
There are various ways to bypass SSL pinning, which requires analyzing the binary code to determine the language it was written in and narrowing down on that language-specific method.
-
Some pinned iOS certificates that are changed regularly need to be updated in the binary code, making the process very cumbersome for the developers.
-
Many organizations don’t like to invest their resources in this area due to the number of loopholes and the lack of preparedness for handling complex systems.
Conclusive: Why Should Hire An iOS App Development Company?
iOS SSL pinning is needed to add an extra layer of protection to the applications. SSL pinning adds more to the existing SSL protocol by verifying the remote server’s certificates with the help of the ones that have already been saved as a local copy in the app bundle.
This technique has some downsides during implementation, including frequent code modifications and certificate expiration. Thus, one should wisely choose their iOS app development service, which can handle all the exceptions and potential threats.
Markovate strives to provide businesses with the best solution possible by utilizing the proper tech stack and cutting-edge technology. Furthermore, as an app development company, we aim to provide businesses with a product with all the desired features, a fantastic UI design, and an impeccable user experience.
We understand that every firm has a unique concept, a fantastic set of needs, and a unique end. We are open to catering to all. Our iPhone app development services are user-friendly, scalable, adaptable, and keep security as a priority.
Our developers are dedicated professionals who specialize in various kinds of app development. Such as iOS, React Native, Hybrid, and UI/UX designing. We ensure that throughout our process, our clients are involved in helping build their vision. From creating interactive prototypes to making the finalized app after integrating all the features and then pushing it to the market and maintaining it, our goal is to make each stage as complete and seamless as possible. If you’re developing an iOS app that incorporates SSL pinning and need assistance with AI integration, Markovate offers AI development services to help you leverage the power of artificial intelligence in your app
iOS SSL Pinning: FAQs
1. Can you bypass SSL pinning?
Bypassing SSL pinning requires creating your certificate, adding it to the mobile, and then tampering with the pinning method. However, a few times, this can be bypassed using hardware that is super easy to set up. And run if the user has enough and adequate knowledge about the same.
2. What is SSL pinning iOS Swift?
SSL Pinning is a method used in Swift. A language used in the iOS platform to prevent dangerous security attacks by pinning trustworthy certificates. This typically allows you to verify the identity and refuse all connections different from the designated server.